OpenClaw grabbed 184k GitHub stars in a month. Rails has 56k after 20 years. But should you really run a daemon with full access to your machine?
The Chameleon With Claws
clawdbot/moltbot/OpenClaw — this chameleon flew through our tight-knit tech world and generated a spectacular amount of hype. 184k GitHub stars in the last month alone. For context, Rails has 56k stars after nearly 20 years.
So what awaits this clawed chameleon — a rapid rise followed by an equally rapid fall?
What It Actually Is
If you boil down what this tool does: it’s a daemon running on your machine that has access to everything on your computer, configured through plain text .md files for whatever tasks you need.
Yes — you voluntarily and responsibly launch a daemon on your PC that has access to everything. Trojans are nervously smoking in the corner.
The Pitch
Say you set up Telegram as the interface. You send a message:
“Check my Slack for unread messages”
And it replies:
You have 3 unread messages from PM Max, here’s the text: “blah blah blah.” What should I reply?
From there, your imagination is the limit — open Jira and update a task status, push the latest commits to GitLab, and so on.
What Makes It Convenient
You get full access to your PC from Telegram (or any other messenger). You can even install a Whisper plugin to dictate prompts by voice, and it’ll break them down into keywords and tasks. Maybe you can even send video messages by now — haven’t checked.
What Makes It Dangerous
As someone who used to uninstall TeamViewer right after every session — just in case someone found a vulnerability and got access to my passwords and private data — this approach is deeply alien to me.
It gets worse: right now there’s essentially one developer who opened this Pandora’s box, while plugins with exploits number in the dozens. He physically cannot moderate all of it — and doesn’t want to. When asked directly about malicious plugins in the registry, the author’s response speaks for itself:
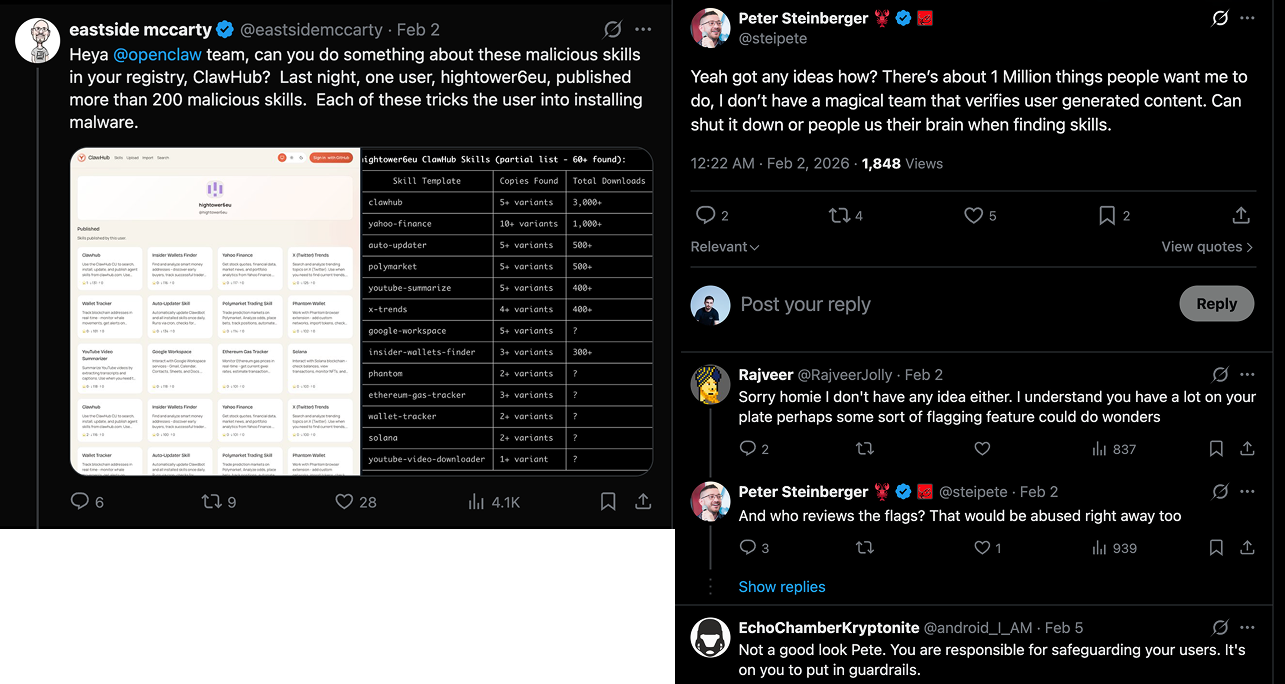
OpenClaw author’s response to security concerns about malicious plugins
Users don’t want to audit every plugin to check whether it contains an exploit or not. The result is an extremely fragile and dangerous construction — but the hype train has already left the station.
The Vacuum Use Case
Realistically, you could use it in an isolated environment. What I mean: a clean Mac Mini that has internet access but no access to sensitive information — no iCloud, no work chats, no password files.
But then what would it actually do? Send you weather forecasts? Google things for you via Telegram?
The use cases are unclear. Meanwhile, the people posting happy x/tweets about how this thing has access to their work machine — with all the NDAs, source code, and corporate email — that makes my hair stand on end. It’ll hit hard later, when the next “plugin” turns out to be full of holes.
In Summary
Hype, hype, hype, and more hype.
